and the distribution of digital products.
Best Practices for Securing Cloud Environments Against Cyber Threats
In cloud computing, cloud security defends architecture, information, and applications against malicious actions. Data security has never been more critical as companies depend more on the cloud for scalability and distant operations.
\ Reflecting the critical need for strong cloud security measures to guard against data breaches, illegal access, and insider threats, a new Cybersecurity Ventures estimate projects global cybercrime expenditures would reach $10.5 trillion annually by 2025.
\ Cyber risks accompany growing cloud systems and call for proactive solutions to match changing hazards and protect important corporate assets.
The Critical Role of Cloud SecurityThe significance of middleware in data integration has increased as cloud computing has become the standard. Applications hosted by a cloud service provider can communicate with one another and exchange large amounts of data because middleware is built to do just that.
\ Nevertheless, malevolent individuals might target this vital communication infrastructure without proper security measures. Consequently, it is imperative to prioritize security within the middleware rather than merely an option.
Common Cyber Threats in Cloud Environments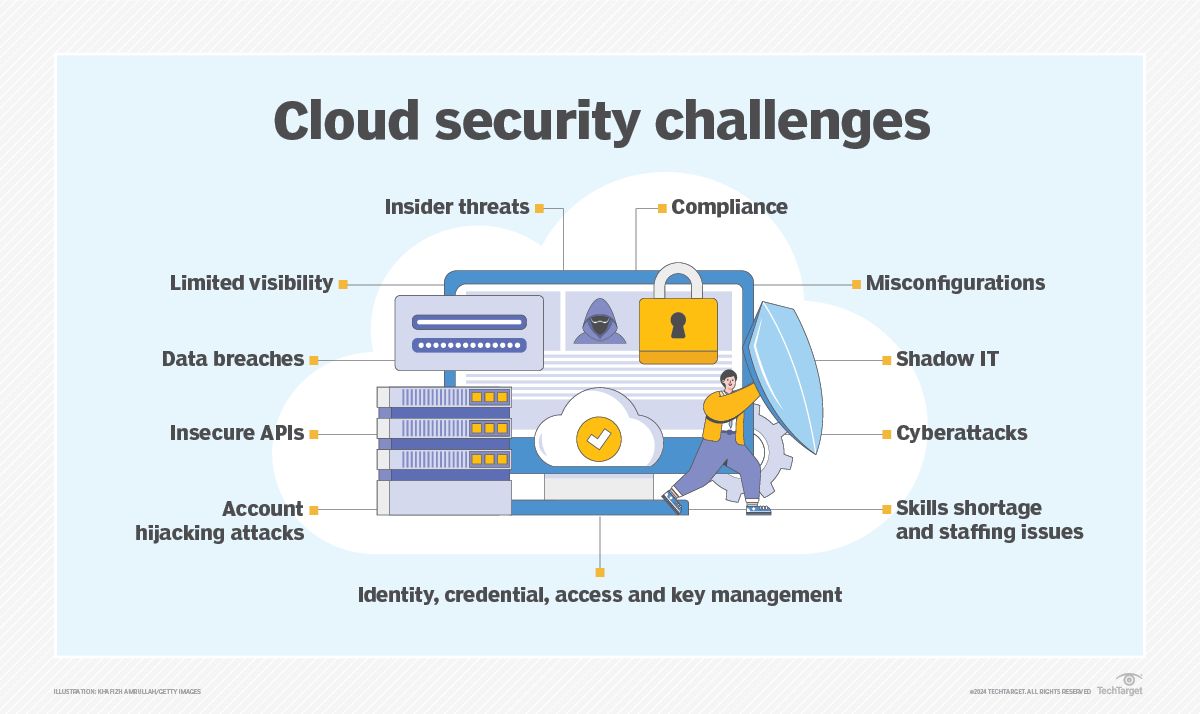
Image: Credit
\ Cloud environments face several prevalent cyber threats:
Data Breaches: These are instances of unauthorized access of a user to certain sensitive data housed in the cloud. 45% of data breaches are said to have involved the cloud, as revealed by a report in 2023.
\
Account Hijacking: This is where attackers can fully take over an account and do unauthorized actions with it. In 2024, a massive case occurred with hacked Microsoft executive accounts, taking away some US governmental organizations.
\
Insider Threats: Data leakage or system compromise may occur due to malevolent or carelessness of authorized users.
\
Misconfigurations: Incorrectly set up cloud resources can expose vulnerabilities. A 2024 study found that 68% of organizations identified misconfiguration as a top cloud security threat.
\
Denial of Service (DoS) Attacks: Overwhelming cloud services to disrupt access.
\ These threats underscore the necessity for robust security measures in cloud environments.
Best Practices for Securing Cloud Environments
Cloud cybersecurity integrates strategies, methods, and solutions. Our 10 cloud data security best practices outline the most effective ways to protect your cloud computing environment:
\
Data Encryption for Enhanced Cloud Security
One of the principal aims of cloud security is ensuring that sensitive data is secured. Data encryption will always be needed in the cloud or at rest to protect such data from unauthorized access or breaches. Such organizations should use the encryption facilities available with the cloud vendors to safeguard encryption keys and securely adopt reasonable key management practices. Protecting data in transit against potential interception through secure protocols is a prerequisite in any networked environment.
\
Regularly Update and Patch Systems
Maintaining a safe cloud infrastructure requires keeping operating systems, software, and cloud infrastructure updated with the most recent security patches and updates. To find, test, and install security updates and patches quickly, organizations should have a strong patch management procedure in place. Integrating AI into systems can reduce vulnerabilities through streamlining and automated enhancement of patching methods.
\
Identity and Access Management (IAM)
Regarding public cloud security, having an IAM solution reduces unwanted access. IAM systems ensure that those with permission can access resources by creating and managing user identities and permissions. Use thorough IAM strategies to enhance security, safeguard private information, and guarantee legal compliance in cloud environments.
\
Leverage Cloud Provider Security Features
Cloud service providers provide several integrated security services and features to improve the security of cloud deployments. Businesses should use these products to safeguard their network traffic and cloud resources, including intrusion prevention systems, security groups, and firewalls, to safeguard their network traffic and cloud resources. To maximize the efficiency of these security elements, proper configuration is necessary. In addition, maintaining current knowledge of new security features offered by cloud providers and incorporating outside security solutions as necessary helps improve the management of the entire cloud security posture.
\
Conduct Regular Security Assessments and Audits
Periodic security checks and various assessments make it possible to eliminate weaknesses, inhibit non-compliance to the set industry requirements, and demonstrate security safeguards in place. Companies must regularly perform risk analysis and penetration tests on their cloud systems to seek probable weaknesses. In addition to the above anomalies, other accreditation bodies such as PCI, HIPAA, CCPA, CSA, APEC CBR, PRP, and GDPR can also be included in the regular follow-up roles, assisting organizations in meeting legal requirements and maintaining the highest standards in the industry. Using constant security monitoring and fast fixing found weaknesses and hazards greatly improves the general state of the cloud environment.
\
Enforce Security Policies and Procedures
Establishing a uniform and standardized method for security requires creating and documenting thorough cloud security policies and procedures. Along with outlining the procedures and controls for safely managing cloud resources, these rules should specify roles, responsibilities, and responsibilities for security-related tasks. Consistently developing security measures and processes throughout the company guarantees compliance with legal and industry standards. It is also essential to regularly evaluate and update these rules to keep up with new technology, developing threats, and shifting business requirements.
\
Implementation of a Zero Trust Architecture
"Never trust, always verify" is the foundation of the cybersecurity approach known as Zero Trust Architecture (ZTA). ZTA views every request as a possible threat, regardless of where it comes from, in contrast to conventional models that place complete trust within the network's perimeter. This lessens the chance of insider threats and the harm caused by perimeter breaches. For example, a company may use micro-segmentation to separate tasks from one another. Unauthorized access by a cybercriminal might only harm a tiny portion of the network, not the whole one. Ignoring ZTA could allow unauthorized access to your network, leading to extensive breaches.
\
Implement Cloud Security Monitoring and Logging
Cloud environments require constant recording and monitoring to identify and address security incidents. Organizations should gather and examine cloud services, apps, and infrastructure logs to find possible security risks or irregularities. Companies can use SIEM (Security Information and Event Management) systems to monitor, correlate, and analyze logs centrally. To lessen the effect of any breaches or attacks, it is essential to establish explicit incident response protocols and respond quickly to address detected security events.
\
Conduct Pentesting
Auditing, penetration, and vulnerability testing all help identify flaws and guarantee industry standards' conformance. These processes ensure the security and reliability of your data and systems, strengthen defenses against online threats, and help you proactively find and address problems.
\
Train Your Staff
Teaching staff members about cybersecurity standards is part of staff training. By effectively identifying and addressing threats, well-trained employees may help organizations protect sensitive data and uphold cloud service security against illegal access by hackers.
| Feature/Provider | AWS IAM | Azure Active Directory (Azure AD) | Google Cloud Identity and Access Management | |----|----|----|----| | User Management | Supports users, groups, and roles | Manages users, groups, and roles | Manages users, groups, and service accounts | | Access Control Model | Policy-based (JSON policies) | Role-Based Access Control | Role-Based Access Control | | Multi-Factor Authentication (MFA) | Supports MFA for users and root accounts | Supports MFA for users | Supports MFA for users | | Integration with External Identities | Supports federation with external identity providers | Integrates with on-premises Active Directory and external providers | Supports federation with external identity providers | | Granularity of Permissions | Fine-grained permissions at the resource level | Fine-grained permissions at the resource level | Fine-grained permissions at a resource level | | Audit and Monitoring | AWS CloudTrail for logging and monitoring | Azure Monitor and Azure AD logs | Cloud Audit Logs |
Bottom LineMaintaining business continuity, guaranteeing regulatory compliance, and protecting private information depends on a proactive cloud security approach. Anticipating and minimizing such hazards helps companies maintain their brand, stop data breaches, and lower financial losses.
\ Using proactive measures, including constant monitoring, frequent security audits, and staff training, companies may keep ahead of changing cyber threats and create a safe and strong cloud environment.
\
- Home
- About Us
- Write For Us / Submit Content
- Advertising And Affiliates
- Feeds And Syndication
- Contact Us
- Login
- Privacy
All Rights Reserved. Copyright , Central Coast Communications, Inc.